ColorTokens, founded in 2015, is a cybersecurity company whose Zero Trust platform gives cloud workloads, dynamic applications and endpoints protection against cyber threats. The platform protects organisations from internal and external threats.
The company’s Xtended ZeroTrust Platform integrates flawlessly with existing security tools to protect enterprise networks against ransomware attacks, unauthorised lateral, and zero-day attacks. The company has built self-learning algorithms to detect, contain, and eliminate threats across data centres and hybrid or multi-cloud environments.
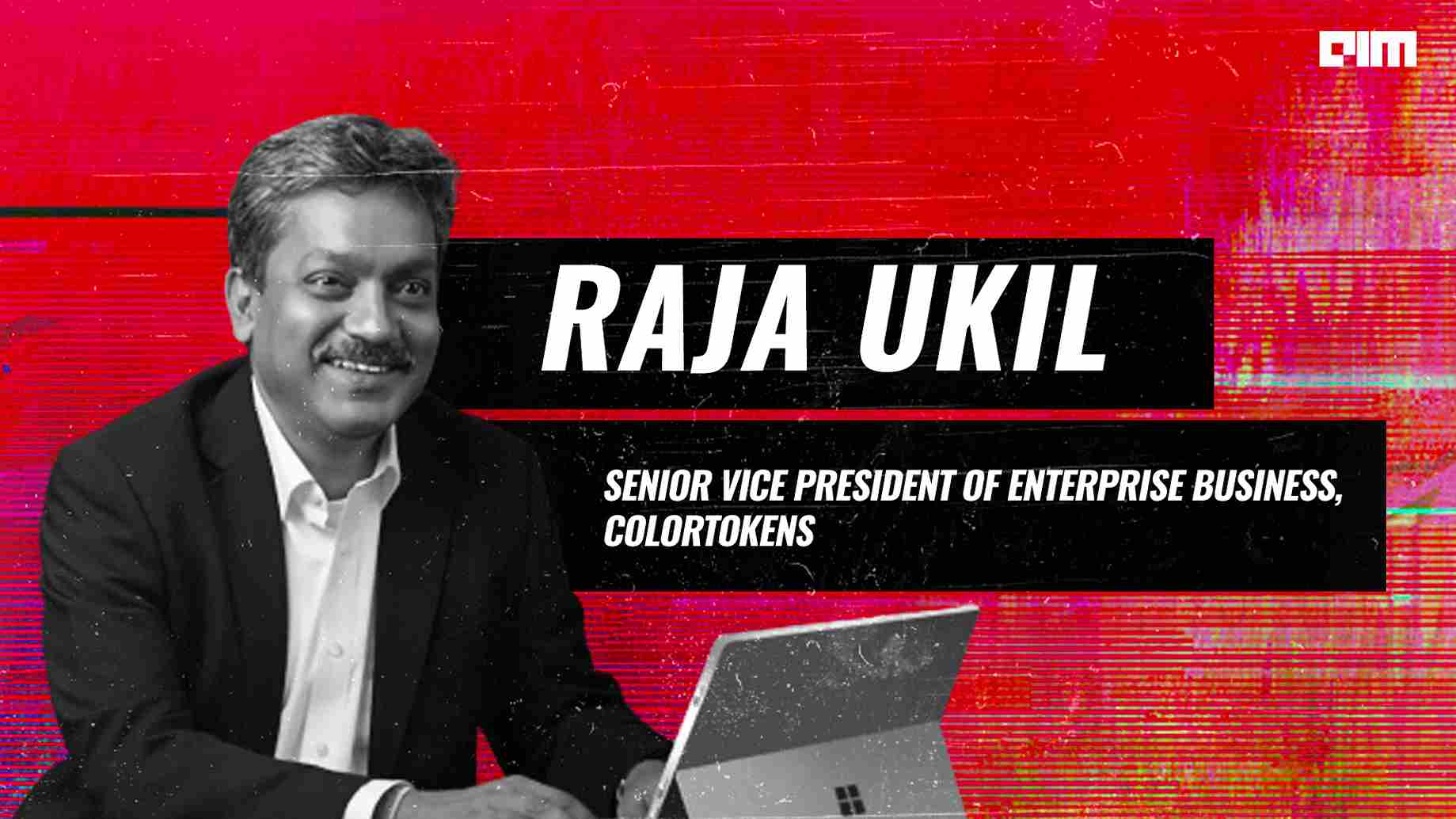
Analytics India Magazine caught up with Raja Ukil, SVP of Enterprise Business at ColorTokens, to know more about its product offerings and expansion plans.
Raja Ukil is the Senior Vice President of Enterprise Business at ColorTokens. Before joining ColorTokens, Raja was the leader and global head of Wipro’s Cybersecurity and Risk Services. At Wipro, he was instrumental in bringing a value proposition that helped the company develop cybersecurity solutions to make organisations resilient against any cyber threats.
A winner of the global CIO 100 awards in 2016 and multiple CIO 100 Hall of Fame in India awards, Raja is also part of the global customer advisory boards of several product companies and startups. He is also a keynote speaker in several industry and technology forums.
Excerpts:
AIM: What exactly is the Zero Trust model your products are built on?
Raja: The Zero Trust Model was coined by Forrester in 2010. Essentially, in this model, any communications that are taking place between applications or devices are not trusted. Both inbound and outbound traffic are blacklisted. Once this is done, critical communications required to run the business are whitelisted. Every connection request from within and outside the network is explicitly authenticated and verified. Back in 2010, there didn’t exist technology that would make the implementation of the Zero Trust Model possible. In 2021, the National Institute of Standards and Technology came up with the proper definition of the Zero Trust Model and the ways to implement it. It has been proven that Zero Trust Model is the most effective way to thwart cyber attacks.
AIM: What were your learnings during the pandemic as an organisation?
Raja: During the first wave of the pandemic, organisations were trying to figure out how to make their employees work from home amid the lockdown restrictions. During the second wave, many organisations migrated to the cloud, and security became paramount as more and more people started working from home. We released our Zero Trust-based Network access solutions during this period. We are seeing constant engagement from various small, medium and large enterprises globally. In India, we are witnessing many organisations adopting cybersecurity solutions.
AIM: How has been your experience selling cyber security solutions in India?
Raja: No technology, solution, or architecture can provide 100% protection against security breaches. However, the Zero Trust architecture is well-established and probably the most effective. In India, there is no mandate, regulation, or culture of reporting security breaches. But in the recent past, the board of directors has started questioning the CEO and the management team about what the company is doing regarding cyber security, which is driving security adoption. Secondly, CIOs of companies have started getting involved in ramping up cybersecurity efforts. Earlier, cyber security was mainly the responsibility of the CISO. However, this is no longer the case with Indian companies. Many organisations in India, including the smaller ones, are looking for genuine advice and technology-driven solutions to bolster their security posture.
AIM: Why did ColorTokens choose the SaaS model of subscription for your solutions?
Raja: We wanted to make the life of our customers simple. We didn’t want our customers to face any deployment challenges with our solution. At the same time, we want to add more capabilities to our platform without causing any disruption to our customers. Also, we want to provide our customers with some predictive validity. We deploy lightweight agents on servers, VM and endpoints. Once it is done, all the predictive analytics is done in the cloud. Unlike hardware-based appliance security, our customers don’t need to worry about meeting prerequisites, which actually adds to the cost and complexity of deploying the solution. Unlike appliance-based security solution businesses that are shrinking on a daily basis, we wanted to future-proof ourselves and decided to go with the SaaS model.
AIM: How do you leverage AI in your products?
Raja: We have built a powerful visualiser that visualises which assets are communicating with each other whether it is from an application to an application, infrastructure to an application, or infrastructure to infrastructure. Secondly, we group things into logical groups when assets are discovered. We have also built a powerful learning engine that studies behavioural interactions to determine what is normal behaviour and recommend policies to the customer. Our platform enables the users to see how things are shaping up and what changes have occurred in their environments. All these capabilities are built on top of our solution.
AIM: How will the threat landscape evolve with the advent of 5G and IoT devices?
Raja: We live in an ‘API Economy’. The world is getting increasingly interconnected with each other. You may never know whether something which is connecting and seeking data from the application is genuine or not. With the advent of 5G and IoT devices, the threat landscape will grow hundreds of folds. Gone are the days when securing the enterprise from the rest of the world by deploying firewalls and intrusion detection systems would suffice. The security perimeter is no longer tied around a data center.
AIM: Why do you choose to focus on providing solutions instead of providing consulting like other cybersecurity firms?
Raja: Most of the customers don’t know where to start their journey as to how to secure their organisations. We see a huge gap in that space, and we are currently focused on helping customers identify those gaps and provide solutions to improve their security posture. However, we have not concluded on whether we want to provide full-fledged services around consulting.