The recent cases of cybersecurity breaches, including the data leak at MobiKwik, Facebook, Juspay, etc, have exposed the chinks in the tech ecosystem.
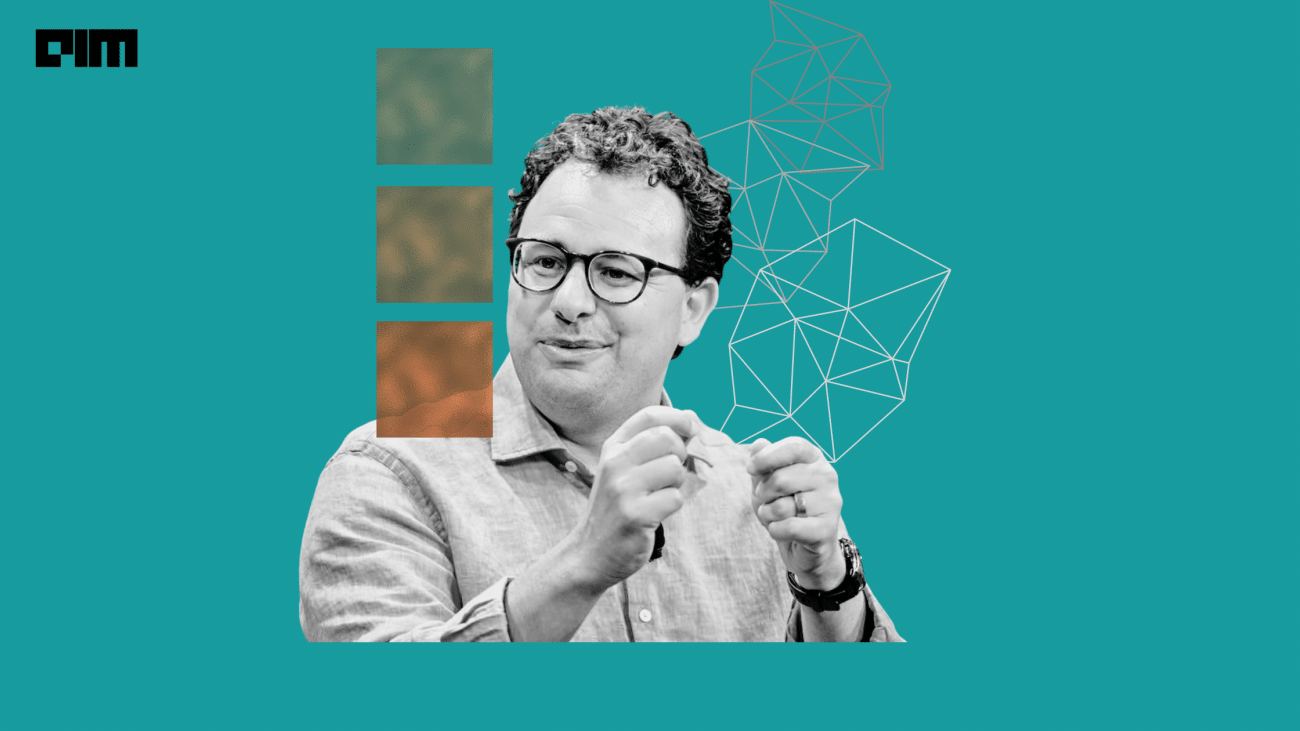
Analytics India Magazine got in touch with Pukhraj Singh, a cyber intelligence and geopolitical analyst with 15 years of experience, to understand the impact of these massive data leaks and how companies can prevent themselves from such losses.
Singh played an instrumental role in incubating the cyber defence operations centre of the National Technical Research Organisation, under the National Security Advisor in the Prime Minister’s Office, India. He is also a member of the Australian Institute of Professional Intelligence Officers. Singh is currently working as the product owner of cyber threat detection at BAE Systems Applied Intelligence (SilverSky).
Edited excerpts —
AIM: 2021 have witnessed massive data leaks of big tech companies, including MobiKwik, Facebook, WhatsApp, Juspay, and many others. What is your take on such an alarming trend?
Pukhraj Singh: First of all, defending against certain data leaks, certain intrusions, or attacks – it’s quite a challenging exercise, even for big companies. The bigger the company is, the more challenging it becomes because the stakes are very high.
For instance, in MobiKwik’s case, it is the way the data leak cases are handled. Typically the information is not disclosed, along with some intelligent denial or underplaying the whole thing, until they are not forced to disclose every bit. This has happened in the past and can happen in the future, which is indeed worrying for us.
Companies must communicate clearly about the breach to their customers and every stakeholder involved during these data leaks. If the companies try to cover such instances, they can swell up and go against them. It is required for the companies to be more transparent about such leaks, which will get them more assistance and add more support from organisations and communities at large.
Secondly, on a broad scale, data leaks are inevitable as we work with these massive databases. The bigger your database, the more lucrative target it becomes. Eventually, companies have to deal with not how and what, but when would it get leaked.
We’ve probably reached a point where most of our information taken by the collectors of these databases would largely be accessible to everyone. Eventually, interfaces are becoming more data-centric.
AIM: How these data leaks impact the big tech companies?
Pukhraj Singh: More than these tech companies, the consumers, including the subscribers and the end-users, are the ones that are massively impacted by these data leaks. For the impacted companies, these situations are unavoidable. Therefore companies need to know the right way to handle such situations. It is imperative for the companies to be transparent about these leaks, for their customers and stakeholders to understand the situation in depth.
Usually, such situations also entail huge reputational damage, which is generally irreversible. A similar instance was witnessed during the Cambridge Analytica case, where Facebook’s reputation has taken a beating. The company was dragged into multiple senate Committees and senate hearings, which ended up being embarrassing for the brand image.
AIM: With your 15 years of experience, what do you think is the cause of these regular data leaks?
Pukhraj Singh: It’s technically very difficult to pinpoint a single reason for these data leaks. I believe it’s just the nature of the beast we’re dealing with.
So, when one creates a massive data collection system to store users’ data, the system will go through multiple interfaces and processes with huge technological architecture. When such complexities are introduced in the architecture to consume data from millions of users in real-time, the complexity itself becomes the company’s weak point.
The complexity is the root cause of insecurity or vulnerability. A defender of the company would have to look at every interface to check and address the weaknesses. Sometimes the cybersecurity experts also miss the broader picture of how the data flows through the whole system. On the contrary, an attacker just needs to find one weak interface to grow its tentacles. So it’s a very different ball game in terms of how the attacker and defender see a company’s cybersecurity landscape.
It’s difficult to generalise, and every breach has a different story. Sometimes, leaks occur via simple ways like password hammering, or sometimes a complicated intrusion like the one we have witnessed in the case of solar winds.
More worrying is the transparency in the response procedures, crisis communications, and these companies’ accountability. Further, India doesn’t have proper agencies to deal with such breaches and leaks, which is another significant concern. The more experience you get, the more you realise that everything is very nuanced, and it’s very difficult to find one short solution to anything.
AIM: What can be done by the tech companies to fix these loopholes apart from playing a blame game or shrugging off the responsibilities? How dangerous can it be for the customers?
Pukhraj Singh: The basic requirement is to change society’s structure to introduce privacy policies to handle data breach and data leaks. For instance, Europe took so many years to come up with its General Data Protection Regulation where they have set up a system, which only deals with privacy, just like we have our Criminal Procedure Code (CrPC) which deals with crime.
So, data leaks cannot be the sole responsibility of one single company because they’re just a part of the problem; they’re not the problem itself. The ecosystem, as a whole, needs to encourage, incentivise and penalise lack of privacy for curbing these data leaks. These cases can be used as an excellent example to make certain broader policy changes around privacy to make the ecosystem more robust. Further, transparency and communication are an absolute must.
It is indeed very alarming and worrying for customers because you can build an entire picture of a person based on his/her data.
The whole nature of intelligence is also turning upside down; intelligence now is not about gaining the secrets of some individual or some organisation, it is rather about joining the dots from public sources. With all of us using some forms of digital payments or having our data on digital platforms, there cannot be any escape from such leaks.
AIM: RBI has asked companies like MobiKwik to have an external forensic audit to avoid such leaks. What more can be done to build a robust mechanism for user’s data protection in the long run?
Pukhraj Singh: Although RBI has asked MobiKwik for an external audit, the auditor would be paid by a client, which creates an underlying conflict of interest. Moreover, many times neutrality of investigation may or may not be there in the first place. Secondly, RBI also has oversight on the auditor, but they will also need expertise in forensics, which again brings in massive complications. Thus, we cannot skirt the issue by just arranging an auditor for the company.
To address such cybersecurity issues, companies need to assign proper cabinet-level attention to introduce privacy frameworks. A long-term strategic vision is critical for the company to deal with advanced level breaches and leaks. Privacy should become like a ministerial priority — just like we have a minister of petroleum and communications. Cybersecurity is definitely becoming a trivial concern that needs proper attention.
AIM: May we know how users at an individual level can protect themselves from these data leaks?
Pukhraj Singh: Cybersecurity on an individual level is a challenging task, as many a time, cybersecurity professionals can also fail to enforce good privacy settings on their mobile phones. The world is increasingly relying on mobile and web applications for their daily life; thus, having good operational security around the systems is no piece of cake.
It all relates to threat perception. One’s privacy has to be subjective to his/her threat perception. Alongside, it’s absolutely challenging to manage a software supply chain where every component is coming from someplace else. Thus, it becomes impossible to investigate the status of underlying hardware and software, as well as to secure databases. The only option is to switch oneself off from the grid or just exit the grid; however, that again isn’t practically viable. Thus, one can work towards minimising their digital footprint.