As the world worries about the attacks like ransomware and DDoS, there are other attacks that are gaining a lot of traction amongst the threat actors. And one such attack that has lately started to make sense is “Paraphrasing Attack”.
What’s A Paraphrasing Attack?
Currently, a significant number of companies are relying on artificial intelligence algorithms to handle text-based content. However, despite the fact that sought-after technologies like AI, NLP, or ML are being used, there are gaps where even they are failing to ensure to complete security. Paraphrasing attacks are mostly focused on AI-powered systems which are in charge of carrying out text-related tasks such as spam filter, analysing the sentiment of social media posts and online reviews, evaluating resumes and detecting fake news. The concept of paraphrasing attack is about making some hard-to-spot changes in the content — here, the threat actor modifies the content in order to bypass these AI algorithms while conveying the same message to the human recipient.
Adversarial Vulnerability With AI
Recent research by IBM, Amazon, and the University of Texas shows how threat actors can attack AI algorithms and manipulate the way we work, using the right set of tools.
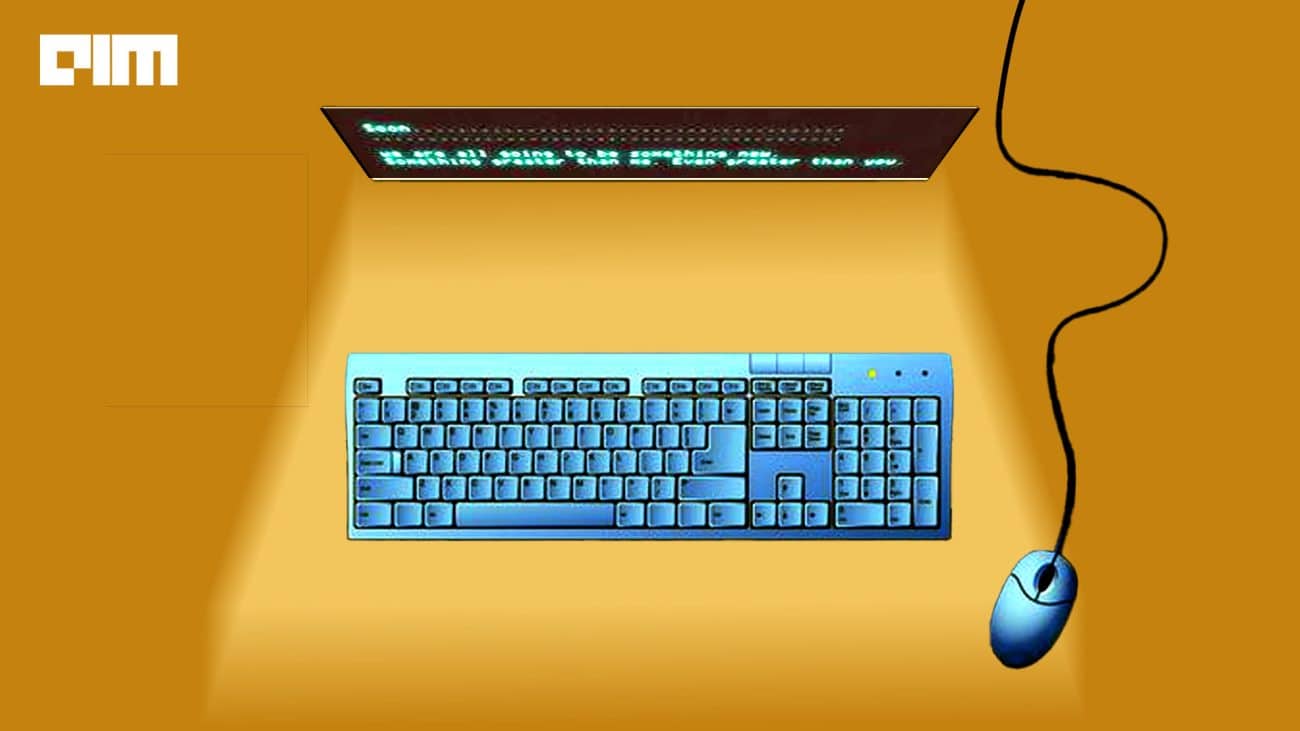
If we look at the previous examples of this kind of attack, they are either carried out by changing one of two words in a sentence. For example, Original Sentence: We are ABC Media company and we want to get in touch with the marketing person of your company.After changing one term: We are ABC Media firm and we want to get in touch with the marketing person of your firm.
However, gone are those days, and new techniques and methods have started to emerge where the things are going one step ahead. The researchers not only tried playing around with words in a sentence but also paraphrased the entire sentence without compromising with the context of the content. For Example, here is the original Sentence: We are ABC Media company and we want to get in touch with the marketing person of your company. And here is the paraphrased sentence: We are ABC Media organization and we need to connect with the advertising individual of your organization.
According to one of the researchers, this method of manipulating the content gives the attack a larger space by creating sequences that are semantically similar to the target sentence.
Amid all the talks around paraphrasing attacks that target AI algorithms, many people have started to dig the major reason behind hackers turning to this form of attack. While many have understood the reasons, there are people who are still looking around.
AI and NLP are like double-edged swords, they can be used by not only developers but also by threat actors and the prime idea behind paraphrasing attacks is to use their powers in an adversarial way. The fact that these algorithms develop their behaviour of filtering things based on a numerous amount of examples, make them vulnerable to adversarial attack. Why? Because it takes has some protocols that it follows, and changes in the protocols would lead them to do something that they aren’t supposed to.
Another major advantage for hackers to go with a paraphrasing attack is the fact that humans cannot detect it because the content holds the same context. Meaning, if the machine fails to detect the email as spam, there are high chances that even human wouldn’t be able to figure out whether the content is genuine. One of the simple examples of a paraphrasing attack instance is when a human sees a typo in an email, s/he thinks it’s just a mistake has nothing more serious in it; however, the scenario could be completely different — it could be a method that is used to bypass the filter.
In Conclusion
Cyberattacks have reached a completely new level with the advent of technologies like AI and ML. These techs are being used for a lot of business operations and threat actors are reverse-engineering them come up with new strategies to compromise enterprises and individuals.
The number of incidents is not that significant at this point, despite the fact that the severity level is high. Now, this recent research would definitely bring some awareness about the potential trouble that the hackers would make if companies and individuals don’t take this threat into consideration and be start looking for ways to cope with it.