|
Listen to this story
|
IBM Red Hat, one of the top providers of enterprise Linux, has been embroiled in a controversy over the past few months. In June, the company decided to put its Red Hat Linux stream behind a paywall, only continuing to open source its CentOS Stream. The RHEL (Red Hat Enterprise Linux) distribution, which was previously open source, now cannot be redistributed even by paying customers.
This not only disrupts the various upstream enterprise Linux distributions, it also creates a rift between Red Hat and members of the enterprise Linux community. This move has brought up the sensitive topics of the betraying of the open source community’s trust and violating the General Public License (GPL) that Linux is built on. However, the paywalling of RHEL belies a deeper issue in the enterprise Linux market — its business model.
RedHat and other Linux providers have been repackaging publicly available Linux distros for use in the enterprise sector and selling them with vendor support. While the latest move might be necessary to keep RHEL as a competitive service, it also shows the greedy nature of Red Hat, amplifying their perceived ‘ownership’ of enterprise Linux.
Enterprise Linux: Stability over security
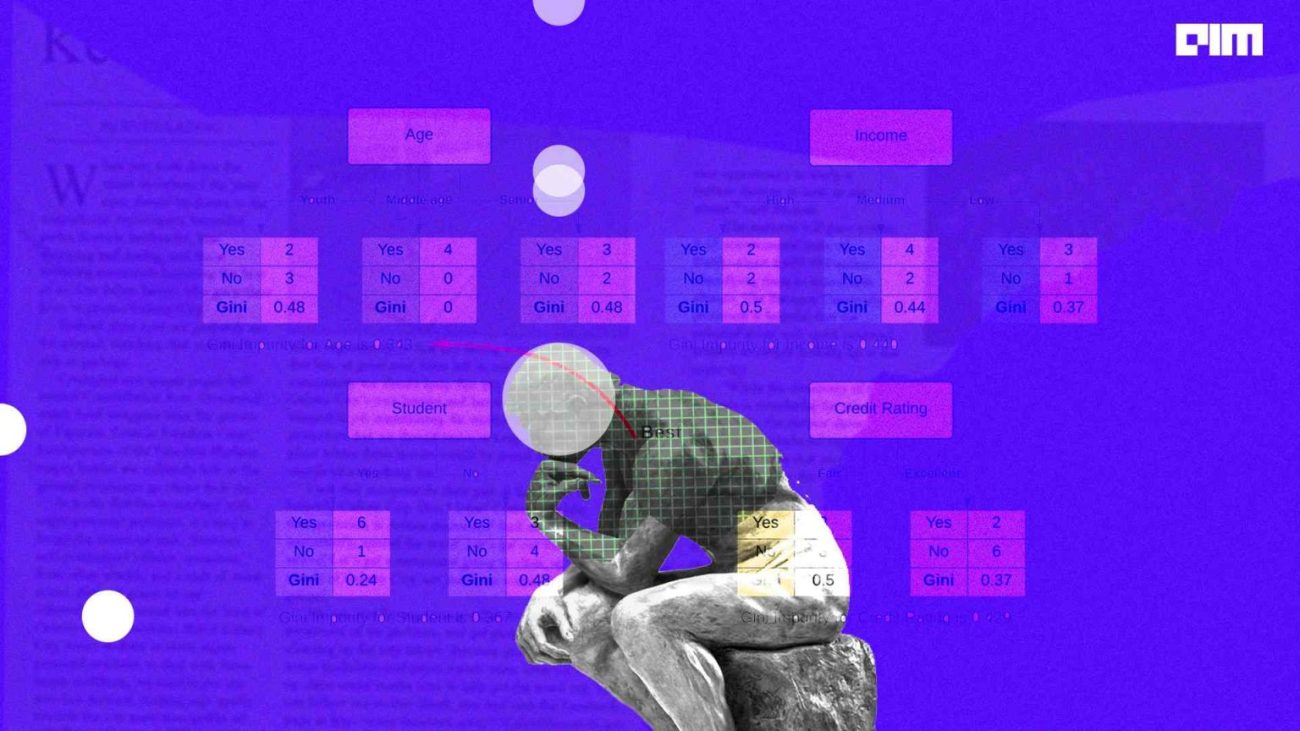
To further understand how enterprise Linux works, we must explore the concepts of upstream and downstream distributions. At the top of the ‘stream’ are the Linux kernel updates, with any other distros being ‘downstream’ or derived from the main Linux kernel. In enterprise Linux, RHEL is usually upstream, with other distributions like Alma Linux, Rocky Linux, and Oracle Unbreakable Linux building out features based on RHEL.
In a nutshell, Linux providers like RHEL and Oracle take the publicly available open source code of Linux and go through it with a fine-tooth comb. They then seed out some of the more problematic bugs, optimising their distros for stability. These kernels are often years-old Linux versions which have been locked to that specific version, usually made for a long-term support model in the timeframe of 10 years.
As the enterprise kernels get updated with new versions and features, enterprise service providers try to keep track of the changes and try to fix any bugs that can arise from the update. However, one of the biggest issues with this model is that security updates usually get delayed for years on end, unless the issue is extremely sensitive.
This tradeoff of stability over security has resulted in Linux becoming a prime target for cyber criminals. According to research, Linux is one of the prime targets for hackers running ransomware campaigns, with attacks on these systems increasing 75% over the last few years. Moreover, researchers also found that ransomware groups are tailoring their attacks to focus specifically on Linux systems.
Cybersecurity researchers at VMWare have also exposed malware in Linux-based multi-cloud environments, shedding light into a new family of ransomware and crypto mining payloads made specifically for Linux. Moreover, key decision-makers view Linux as generally more secure than Windows, resulting in a lack of focus on threat management for Linux systems.
This has created an environment where Linux servers are becoming prime targets for attacks, with enterprise Linux providers sorely lacking in providing security updates to the ecosystem. Adding to this, RHEL’s move to put its Linux distribution behind a paywall might end up causing a domino effect in the enterprise Linux space.
The way forward
“I feel that much of the anger from our recent decision around the downstream sources comes from either those who do not want to pay for the time, effort and resources going into RHEL or those who want to repackage,” said Mike McGrath, the vice president, core platforms engineering at Red Hat, defending the company’s decision to paywall the RHEL source code.
Other enterprise service providers have also spoken out against Red Hat. Oracle, which offers both a Red Hat Compatible Kernel (RHCK) and its own distro called Unbreakable Enterprise Kernel (UEK), has been the most vocal against this change.
“IBM doesn’t want to continue publicly releasing RHEL source code because it has to pay its engineers? That seems odd, given that Red Hat as a successful independent open source company chose to publicly release RHEL source and pay its engineers for many years before IBM acquired Red Hat in 2019 for $34 billion,” said Edward Screven, Oracle’s chief corporate architect, and Wim Coekaerts, head of Oracle Linux development.
While issues of monetisation can only be shed light upon by parties close to the matter, closing off the source code for a product which is inherently built for stability over security is a recipe for disaster. Now that there are fewer parties working downstream of the RHEL code to make it more secure, the onus falls on Red Hat to make enterprise Linux safer.
To overcome this issue, enterprise linux service providers must move towards a release schedule that more closely tracks the mainline Linux kernel, as opposed to being downstream of other enterprise Linux distros like RHEL. A good example of this is Oracle’s Unbreakable Enterprise Kernel (UEK).
While UEK first started off as a downstream fork of RHEL, it has now become an enterprise Linux kernel that closely follows the upstream Linux kernel. By taking an approach that allows the maintainers to lag behind mainstream releases, Oracle has enough time to perform ‘enterprise grade’ validation and to even carry out stringent bug tests, ensuring both stability and security.
This approach is the best way for enterprise Linux to finally begin focusing on security, especially considering the current cybersecurity risks that older deployments face.