Golden Globe award-winning actor Rami Malek plays the role of Elliot Alderson in the critically-acclaimed TV series Mr Robot (2015-). As a part of the group called “fsociety” he is targeting the downfall of E-Corp, the company which killed his father. Elliot uses a number of hacks throughout the series and is no hacker to mess with. But the best part is that the show is not just popular for its thrilling storyline, but also for its remarkable accuracy of the use of technology. The award-winning series just announced its final season last month, which is set to release this year.
Viewers, especially from the tech fraternity, can exactly understand the nitty gritty behind the technology portrayed in the series. In this article, we will take a closer look at the various hacks that the protagonist from Mr Robot uses and how realistic they are in the real world:
Technology From The Mr Robot
The show has many instances of real-life tools and tricks. Following are some examples which are so accurate to the real world that they are highly appreciated and makes it obvious for the show to be the hit that it is.
Kali Linux: The show features Kali Linux used by Eliot very frequently. The distro of Linux is popularly the hackers choice of OS since it has many security testing tools and allows the use of similar tools and techniques that a hacker would use to test the security. In Sseason 1, Elliot uses a Raspberry Pi to jack up the temperature in an offsite storage room where E-Corp has its data stored on magnetic tapes.
Hacking Passwords: Eliot hacked a number of accounts with just guessing the passwords. He gets access to the information of both acquaintances and strangers by using brute force, which is a trial and error method used by application programs to decode encrypted data such as passwords or Data Encryption Standard (DES) keys. Using a program, brute force tries all possible combinations of characters until it finds a match, or using a simpler version of it called a dictionary attack. The more popular and simpler the combination of characters and words, the faster the program will discover it. Eliot hacks many accounts by this method, he hacks his therapist’s password and also of his colleague Ollie Parker and he easily gains access to all the other accounts after one successful hack. This brute-force attack was also used by Elliot against Tyrell Wellick.
Anonymous Internet Activity: A character called Trenton uploads a leaked FBI conference using the Tor Browser, which is popular for anonymous internet activity. It is basically developed originally for the US Navy and was further advanced by DARPA. In spite of this, Tor is used in credit card fraud and black market drug trades and has a few areas of weakness that can lead those with limited IT security training into very dangerous territory.
Extracting Passwords: Angela from Mr Robot is shown using mimikatz on a USB Rubber Ducky, which is a USB device that emulates a USB keyboard, as a backup plan in case she can’t pull off the femtocell hack. Mimikatz is a post-exploitation tool that bundles together some useful tasks that hackers may want to preform. The Rubber Ducky simply has its firmware flashed with the code of a device and so any system that it plugs into will automatically receive input from the Rubber Ducky, just as it would with any device attached to that system. A USB device can indeed be used to extract passwords from a Windows machine in clear text, just the way Angela did in the scene.
ProtonMail: ProtonMail is a secure, end-to-end encrypted email service based in Switzerland. The TV series researched secure email services to such an extent that the influenced the development of their security software. The team had asked the ProtonMail developers if it was possible for users to monitor their own email activity in ProtonMail because that is what a security-focused character of Eliot would want.
This triggered the idea to the ProtonMail developers and they implemented this feature in their v2.0 version of ProtonMail.
Spoof SMS: Elliot uses Social-Engineer Toolkit’s SMS spoofing function to get a supervisor to leave Steel Mountain because she had suspected him of planting a Raspberry Pi in the office and also so that he can move around in the facility on his own. The Social-Engineer Toolkit (SET) exists in real life as well and is specifically designed to perform advanced attacks against the human element. On the show, Elliot’s fsociety comrades have shown using Kali to send the spoofed SMS, something which is possible to do in the real world.
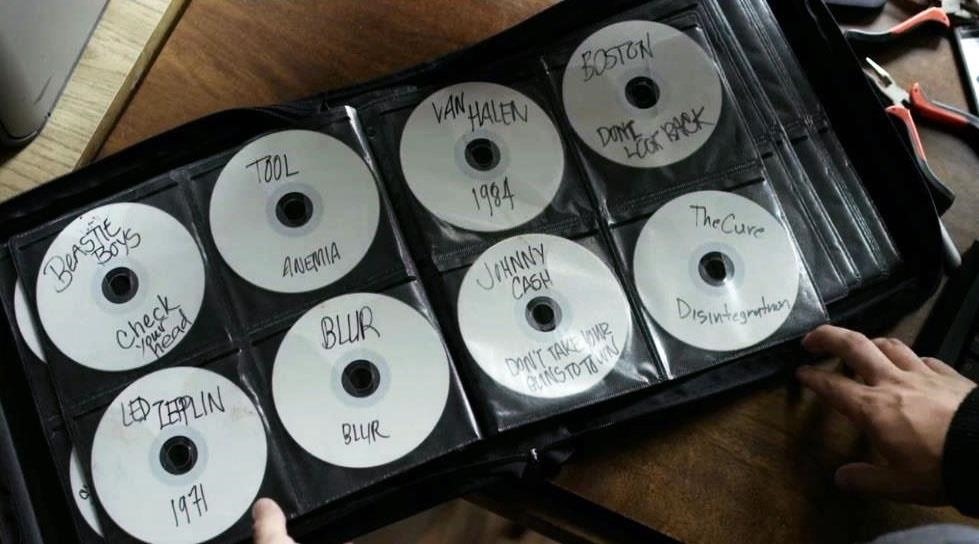
Encrypted Information In CDs: It is seen that Eliot is copying music to some set of CDs and labelling them with band names, embedding encrypted information on them that only he can decode. Anyone else who plays these CDs will only hear the audio, not the hidden information. He saves data of his acquaintances from anyone else. This is an actual practice called steganography and he uses DeepSound software package for this.
Espionage and terrorist organizations have been using these techniques for many years. Reportedly, Al Qaeda used these techniques to hide messages on their website to their followers in the 1990s and 2000s.
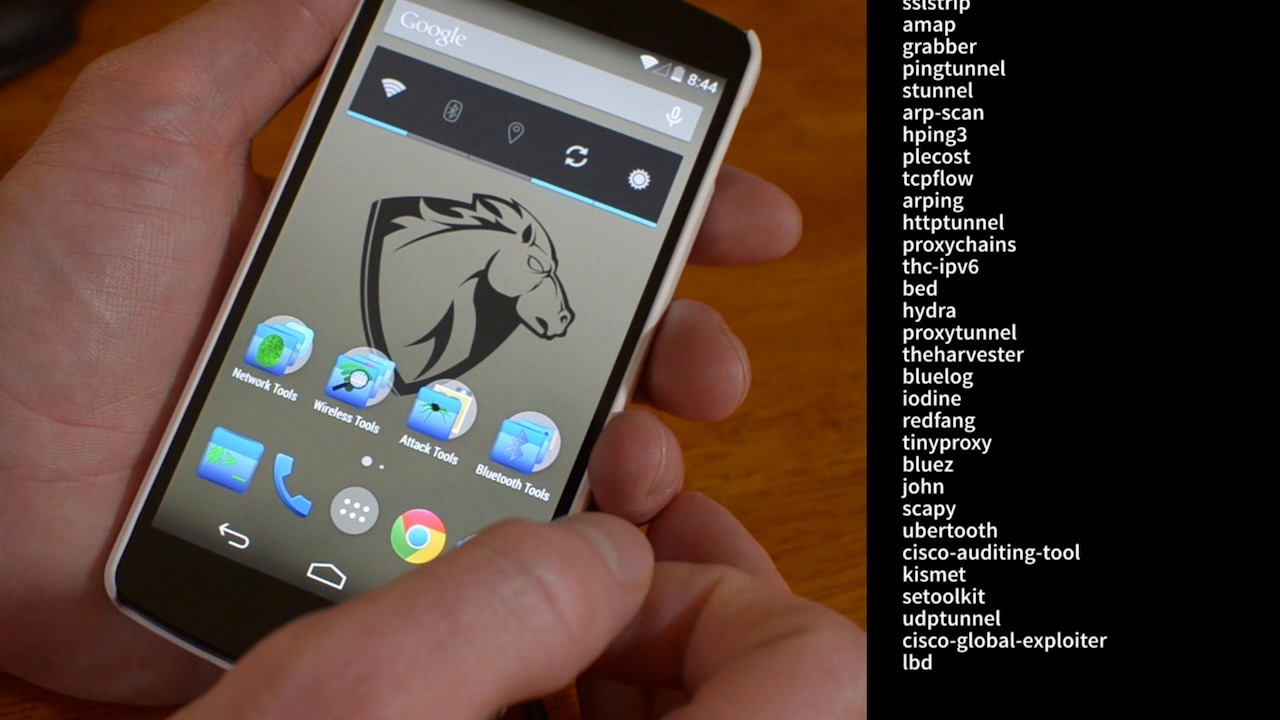
The Pwn Phone: Elliot is seen using a Pwn Phone as a mobile platform to run a custom script he has written called CrackSIM, whose goal is to find vulnerable SIM cards and then cracking the DES encryption of that card. Elliot then loads a malicious payload onto the SIM card. The Pwn Phone is an LG Nexus 5 phone that doubles as a powerful penetration-testing device.
It is built for penetration testers for network hacking and security. Elliot uses a Pwnie Express Pwn Phone – which has Pwnix pre-installed so that he and his sister Darlene can tap into the Dark Army’s phone calls.
The Real Hackers
The makers of Mr Robot have had a thorough study of the tricks and hacks presented and it is incredible that they could pull it off so fluently.
“One thing I’ve noticed about the show is that it feels like a period piece of today,” Sam Esmail, the creator of the TV series had said. “The world is so heavily influenced by technology and it has started to feel like it’s not on solid ground. The world has become unreliable, unknowable. Facts are vulnerable and things you have come to rely on are no longer there. It’s an overlap that I’m not going to be so bold as to say I predicted, but that was what I was thinking about when I constructed the character of Elliot.”
It even makes sense because Esmail began writing his code after he got his first computer at 9 and has worked in the New York University’s computer lab as well.
“I wanted to tell a story about hacking … and I was watching all this cheesy crap. They’re not great at representing what that world looks like, and what hacking looks like, which is not cheesy graphics and ones and zeroes flying at you,” Esmail had said during a panel discussion. Esmail described familiarizing himself with the technology world by reading blogs in order to figure out “what was plausible and what wasn’t.”
Kor Adana, the writer and technology producer has also had a full-time day job at Cybersecurity and can hence give justice to the plot. He had said that they’re completely plausible. Adana’s background is in cybersecurity, and he works with a team of experienced hackers to develop the technological storylines for Mr Robot. Together, they ensure that even on-screen IP addresses, URLs, and QR codes lead viewers to real destination.
Mr Robot fans are now waiting for the upcoming season, which, sadly, has been confirmed will be the final season of the dystopian hacker suspense thriller. But what Mr Robot has brought us through these three years, paying granular attention to the real world resemblance have been incredible and tech geeks sure love shows like this so they will forever mark an everlasting impression on the audiences.